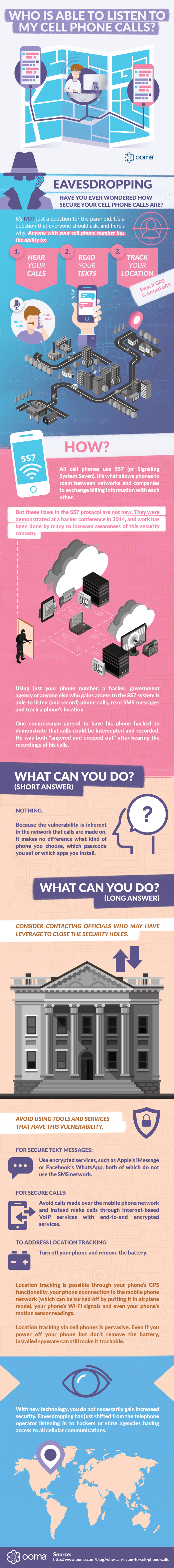
Who Did You Say Is Listening to My Cell Phone Calls?

Have you ever wondered how secure your cell phone calls are, or wondered if someone could eavesdrop on what you were saying?
It’s not just a question for the paranoid. It’s a question that everyone should ask, and here’s why.
Anyone with your cell phone number has the ability to hear your calls, read your texts and track your location (even if GPS is turned off).
Paste this Image on Your Site!
Simply copy and paste the code below and you can share this infographic on your site:
How?
It’s shocking how little privacy we have with our cell phones, and the root of this transparency is a functionality that’s embedded into how our phones work. Let’s take a look at the technology that lets anyone listen to our phone calls.
All cell phones use SS7 (or Signaling System Seven). It’s what allows phones to roam between networks and companies to exchange billing information with each other.
A doorway in the SS7 protocol gives a hacker unprecedented access to cell phone activities. Using just your phone number, a hacker, government agency or anyone else who gains access to the SS7 system is able to listen (and record) phone calls, read SMS messages and track a phone’s location.
But these flaws in the SS7 protocol are not new. They were demonstrated at a hacker conference in 2014, and work has been done by many to increase awareness of this security concern. One congressman agreed to have his phone hacked to demonstrate that calls could be intercepted and recorded. He was both “angered and creeped out” after hearing the recordings of his calls.
What can you do? (Short answer)
Nothing.
Because the vulnerability is inherent in the network that calls are made on, it makes no difference what kind of phone you choose, which passcode you set or which apps you install.
What can you do? (Long answer)
Consider contacting elected officials who may have leverage to close the security holes. “Mobile networks are the only place in which this problem can be solved. There is no global policing of SS7. Each mobile network has to move — to protect their customers on their networks. And that is hard,” said Karsten Nohl, a German hacker.
As to things you can do on your cell phone to protect yourself, avoid using tools and services that have this vulnerability.
For secure text messages: Use encrypted services, such as Apple’s iMessage or Facebook’s WhatsApp, both of which do not use the SMS network.
For secure calls: Avoid calls made over the mobile phone network and instead make calls through Internet-based VoIP services with end-to-end encrypted services.
To address location tracking: Turn off your phone and remove the battery. Location tracking is possible through your phone’s GPS functionality, your phone’s connection to the mobile phone network (which can be turned off by putting it in airplane mode), your phone’s Wi-Fi signals and even your phone’s motion sensor readings. Location tracking via cell phones is pervasive. Even if you power off your phone but don’t remove the battery, installed spyware can still make it trackable.
With new technology, you do not necessarily gain increased security. Eavesdropping has just shifted from the telephone operator listening in to hackers or state agencies having access to all cellular communications.
As hacker and security company founder John Hering explains: “In today’s world, there’s really only two types of companies or two types of people, which are those who have been hacked and realize it, and those who have been hacked and haven’t.” He added, “We live in a world where we cannot trust the technology that we use.”



